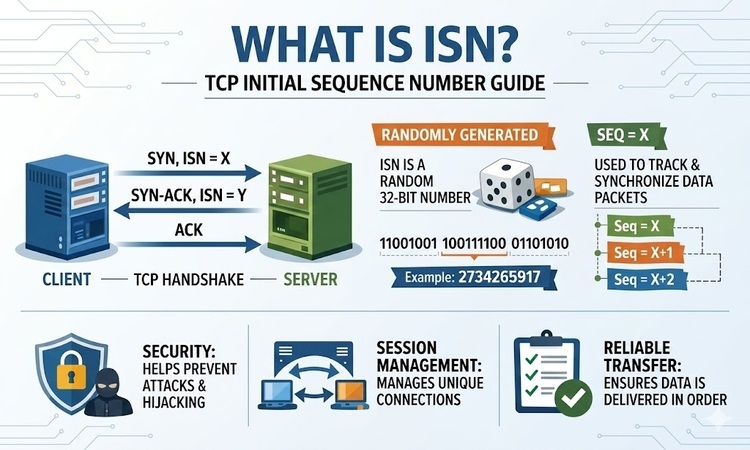
What is ISN? (TCP Initial Sequence Number Guide)
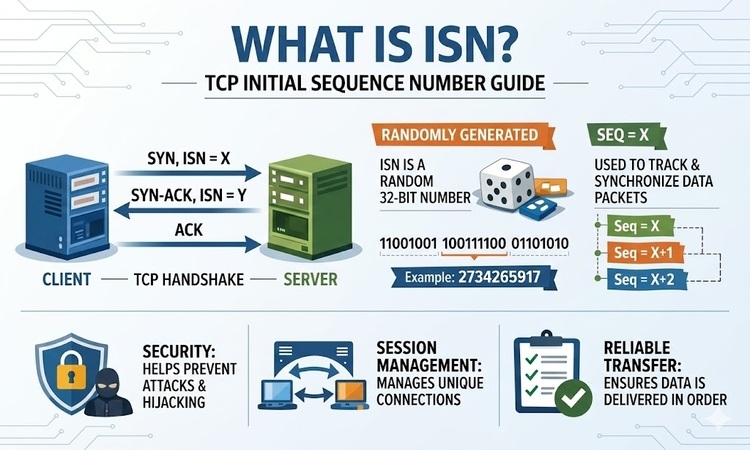
The Initial Sequence Number (ISN) is a 32-bit random value that marks the starting point for sequence numbers in a TCP connection. Exchanged during the “SYN” phase of the three-way handshake, the ISN ensures reliable data reassembly, prevents interference from delayed “ghost” packets, and protects against TCP sequence prediction attacks.
How the TCP Handshake Uses ISN
A TCP connection is established through a three-step negotiation where both the client and server agree on their respective starting points.
- 1. SYN (Synchronize): The Client generates a random ISN ($x$) and sends a connection request.
- 2. SYN-ACK: The Server acknowledges the Client’s number ($ACK = x + 1$) and sends its own unique ISN ($y$).
- 3. ACK (Acknowledge): The Client acknowledges the Server’s number ($ACK = y + 1$).
The Phantom Byte Rule: Although the SYN flag carries no actual data, it consumes exactly one sequence number. This ensures the acknowledgment is mathematically unique to that specific request.
Why ISNs Must Be Random: The “Ghost Packet” Threat
If every connection started at zero, data corruption would be rampant.
- The Conflict: A packet from an old connection (Sequence #500) gets delayed in a router.
- The Crash: A new connection starts between the same two devices. If it also starts at 0, the receiver would mistake the old “ghost” packet #500 for new data.
- The Solution: Modern TCP uses high-range, randomized ISNs (e.g., starting at 2,000,000,000) so that delayed packets from previous sessions are immediately rejected as “out of bounds.”
Security: Defending Against Session Hijacking
In the early days of the internet, ISNs were predictable (linear counters). This allowed attackers to guess the next number and “inject” malicious data into a connection—a TCP Sequence Prediction Attack. Modern Operating Systems now follow RFC 6528, generating ISNs via a cryptographically secure hash of the IP addresses, port numbers, and a secret system key:
$$ISN = M + F(local\_ip, local\_port, remote\_ip, remote\_port, secret\_key)$$
2026 High-Speed Networking Update: The Wrap-around Problem
On modern 10Gbps+ networks, the 32-bit sequence number (4.2 billion possibilities) can “wrap around” and return to zero in less than 4 seconds. To handle this, TCP uses PAWS (Protection Against Wrapped Sequence numbers), which adds a high-resolution timestamp to the header to distinguish “new” low numbers from “old” high numbers.
FAQ: TCP Initial Sequence Numbers
Why does Wireshark show my ISN as 0?
This is a feature called Relative Sequence Numbers. Wireshark subtracts the true ISN from all future numbers to make them easier for humans to read. In reality, the number is a massive 10-digit random integer.
Is the ISN chosen by hardware or software?
The ISN is generated by the Operating System’s Kernel (the network stack). Because each OS uses a slightly different generation algorithm, ISNs are often used in “passive OS fingerprinting” to identify if a device is running Windows, Linux, or macOS.
Does a large ISN slow down my connection?
No. Whether the ISN is 1 or 4,000,000,000, it always occupies exactly 32 bits in the TCP header. It has zero impact on bandwidth or latency.
Can two connections have the same ISN?
While mathematically possible ($1 \text{ in } 2^{32}$), the combination of random port numbers and system secret keys makes the probability of a “collision” causing an error effectively zero in practical networking.